The Geometric Intuition That Makes ECC Hard to Break
Elliptic curve cryptography is the modern default for public-key operations — it is the algorithm behind Ed25519 SSH keys, ECDH in TLS 1.3, and the signatures that secure HTTPS certificates. The reason ECC gives equivalent security to RSA with keys 10 times smaller is that the underlying hard problem — the elliptic curve discrete logarithm — has no known sub-exponential algorithm, unlike integer factorization. Understanding why requires a brief visit to the geometry of elliptic curves.
What an Elliptic Curve Is
An elliptic curve is defined by an equation of the form y^2 = x^3 + ax + b over a field, with the constraint that the curve is smooth and has no self-intersections or cusps (the discriminant is nonzero). Over the real numbers, this looks like a smooth sym
The Group Law: Adding Points on the Curve
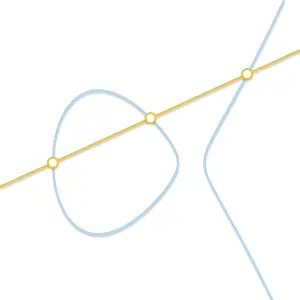
The group law defines how to add two points P and Q on the curve. Draw a line through P and Q — it intersects the curve at a third point R prime. Reflect R prime over the x-axis to get R. The rule is P + Q = R. This operation is closed (the result is alwa
Scalar Multiplication Is the Hard Direction
Given a point P and an integer k, computing k*P — adding P to itself k times using the double-and-add algorithm — is fast. With 256-bit k values, it takes about 256 doublings and 128 additions on average. But given P and Q = k*P, finding k — the elliptic
RSAkey size for 128-bit security
ECCkey size for 128-bit security (Curve25519)
Curve25519 and Its Design Choices
Curve25519, designed by Daniel Bernstein, uses the prime 2^255 - 19 chosen because arithmetic modulo this prime is exceptionally efficient on 64-bit hardware. The curve is a Montgomery curve, which admits a particularly fast scalar multiplication algorith
The NIST P-256 curve is widely deployed but has a controversial history: its parameters were generated using a seed value (c49d3608 86e70493 6a6678e1...) with no explanation of how that seed was chosen. This raises the theoretical possibility of a trapdoor — parameters deliberately chosen to weaken the curve in ways only the designer knows. Curve25519 and brainpool curves were designed with fully transparent parameter generation. For new deployments where you control the algorithm choice, prefer
Go Deeper: Digital Signatures with Ed25519
Elliptic curves over finite fields form an abelian group — and you can build a digital signature scheme on that group. Ed25519 is the signature algorithm that fixed the dangerous random-number requirements of its predecessor ECDSA, by computing its nonce deterministically from the message. Understanding how Ed25519 works explains why it is the right choice for SSH keys.